The SABSA Framework: Risk-Driven Enterprise Security Architecture
By Meravytes | May 26, 2026
The Sherwood Applied Business Security Architecture (SABSA) framework is a comprehensive, risk-driven methodology for developing enterprise security architectures that are explicitly aligned with business objectives.

Supply Chain Attacks: Exploiting Trust in Modern Digital Ecosystems
By Meravytes | April 26, 2026
The central challenge is no longer just defending internal assets, but managing distributed trust across a complex ecosystem.

OpenClaw AI Agent Flaws: When Prompt Injection Becomes a Data Exfiltration Engine
By Meravytes | March 26, 2026
Recent analysis of OpenClaw-style agents highlights a critical issue: prompt injection can be weaponized into full-scale data exfiltration.
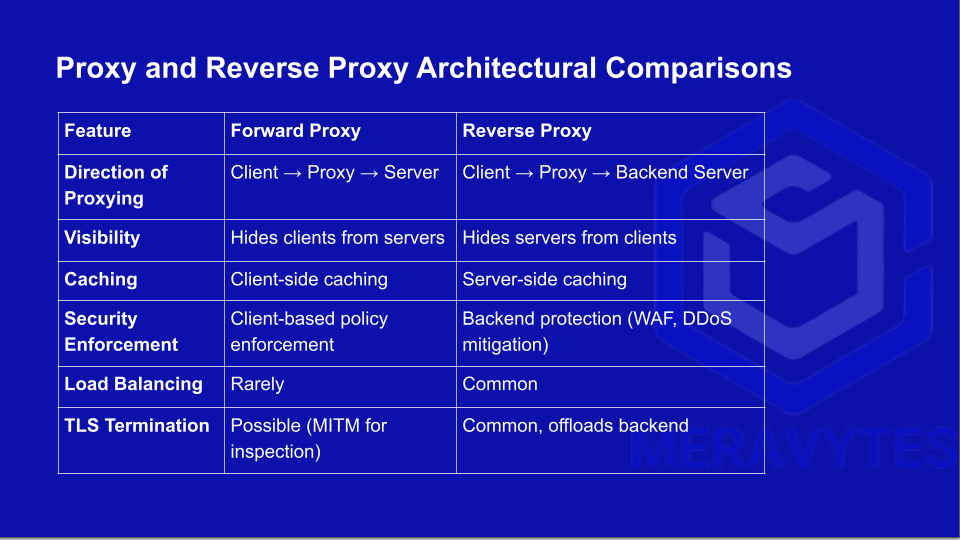
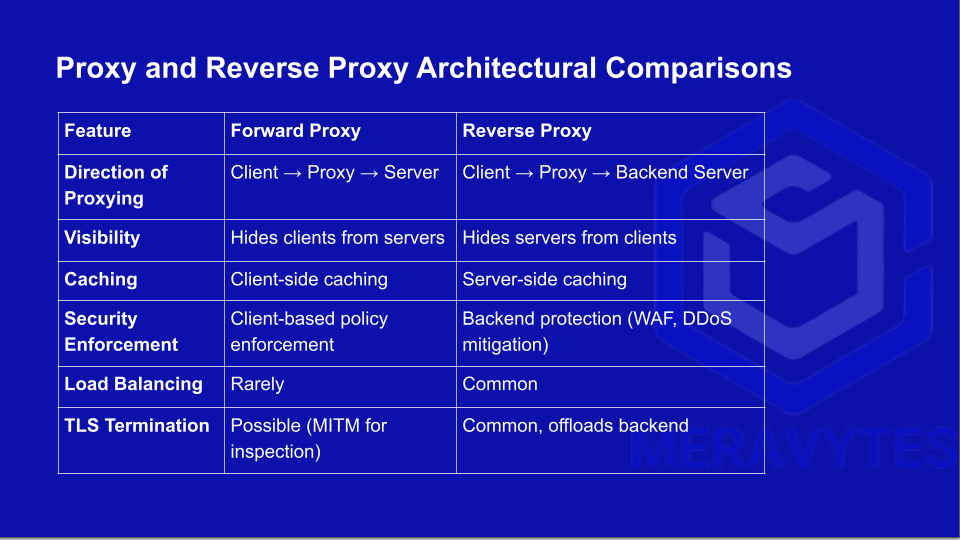
Advanced Analysis of Proxies and Reverse Proxies in Network Security
By Meravytes | February 26, 2026
Proxies and reverse proxies are not merely intermediaries for network traffic, they are strategic points for performance optimization, security enforcement, and traffic orchestration.

ISO 22301 BCMS Implementation
By Meravytes | January 26, 2026
Follow the PDCA cycle and reflect recognized good practices for translating ISO 22301 requirements into practical implementation activities

Mail Gateways: Architecture, Functions, and Strategic Importance
By Meravytes | December 26, 2025
Mail Gateways provide a centralized, policy-driven security layer between internal messaging environments and the public internet.

Cloud Security Posture Management (CSPM) in Multi-Cloud and Hybrid-Cloud Environments
By Meravytes | November 26, 2025
CSPM has emerged as a foundational capability to continuously assess, monitor, and remediate security risks across cloud environments.

Memory Forensics in Action Using Volatility
By Meravytes | October 26, 2025
Among the most widely used frameworks for memory forensics is Volatility, an open-source tool that provides deep insight into live memory images.

Building an Effective SOC: Objectives, Components, and Best Practices
By Meravytes | September 26, 2025
A modern Security Operations Center (SOC) must balance technology, automation, and human expertise to stay ahead of evolving threats.
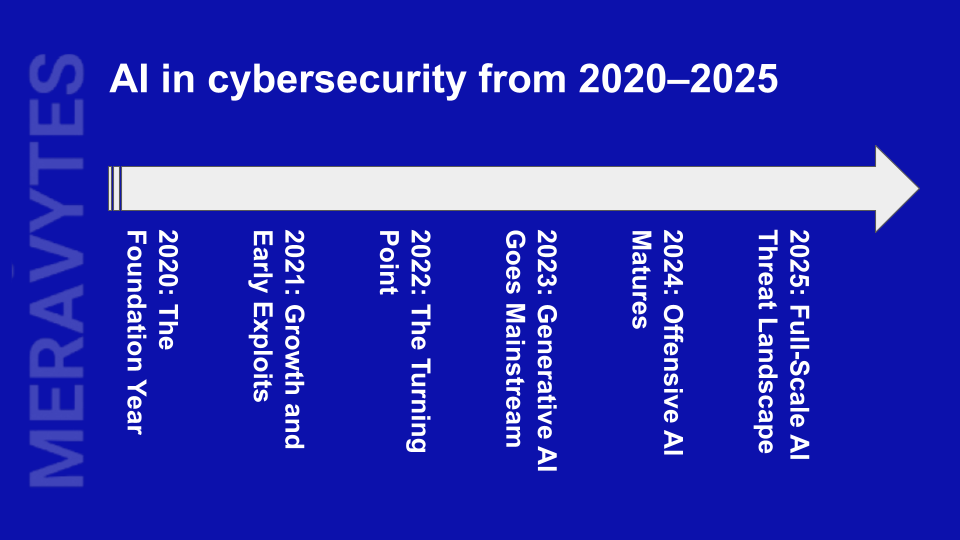
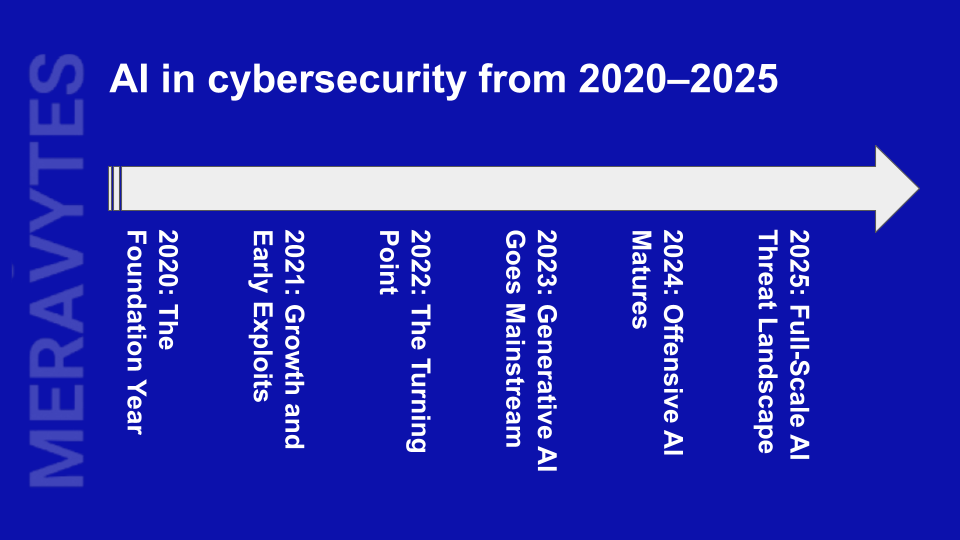
AI-Powered Cyberattacks: The Next Frontier in Digital Threats
By Meravytes | August 26, 2025
AI-powered cyberattacks are rapidly evolving, marking a dangerous shift in the cyber threat landscape.

DNS Zone Transfer: Concepts, Mechanism, and Security Implications
By Meravytes | July 26, 2025
This article explores DNS zone transfer in depth - its purpose, types, how it works, and how to secure your DNS infrastructure against unauthorized access.
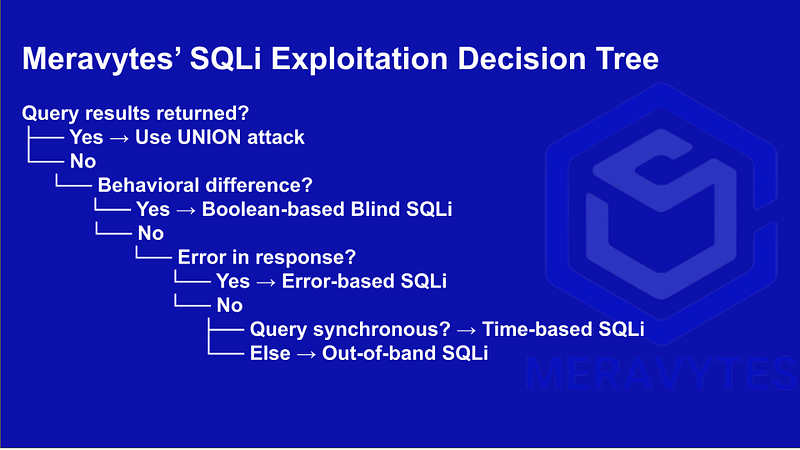
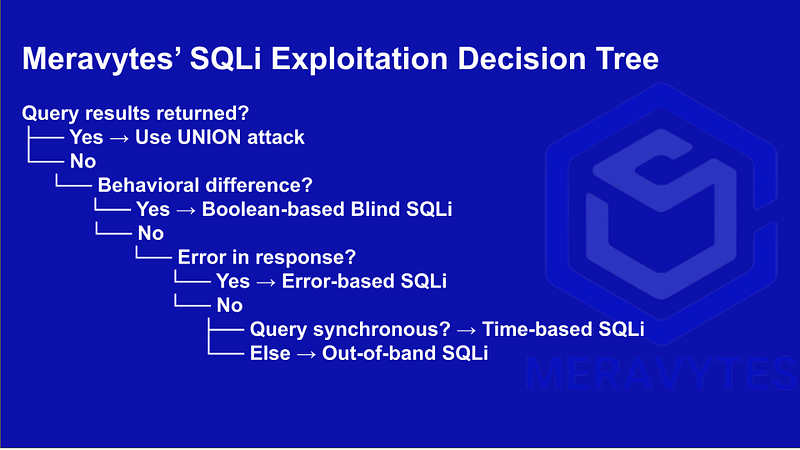
SQL Injection (SQLi): A Comprehensive Guide
By Meravytes | June 26, 2025
This article covers detection techniques, injection points, exploitation strategies, and preventive measures.

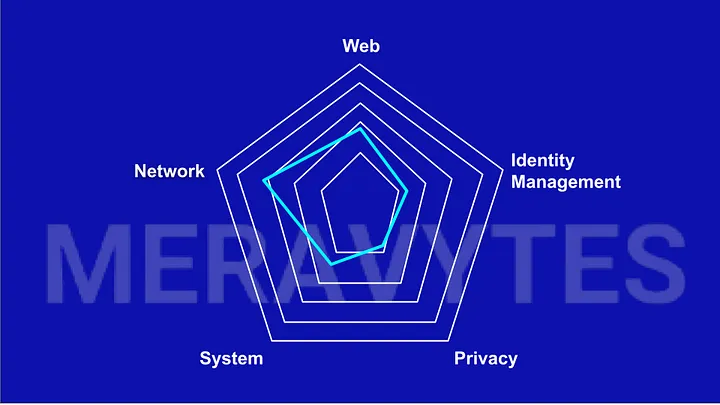
Comprehensive Recon Guide
By Meravytes | May 26, 2025
This article explores the different methodologies, tools, and techniques used in recognition and information gathering to ensure a successful penetration test.
Cybersecurity Audit Vault
By Meravytes | April 26, 2025
We’ll shift the focus away from the usual pentesting techniques or tricks and dive into the critical but often overlooked aspects of auditing: documentation and reporting.

Bug Bounty 101
By Meravytes | March 26, 2025
A bug bounty is a program where organizations reward individuals for discovering and reporting vulnerabilities or bugs in their software, systems, or networks.
A Comprehensive Guide to FortiSIEM System Assessment
By Meravytes | February 26, 2025
This article outlines the tests to be conducted as part of a system assessment for the FortiSIEM solution.
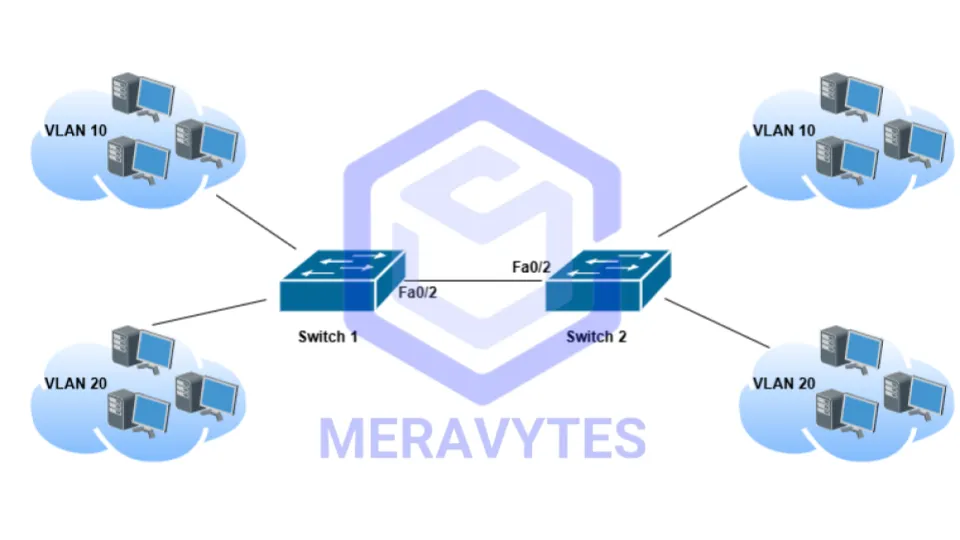
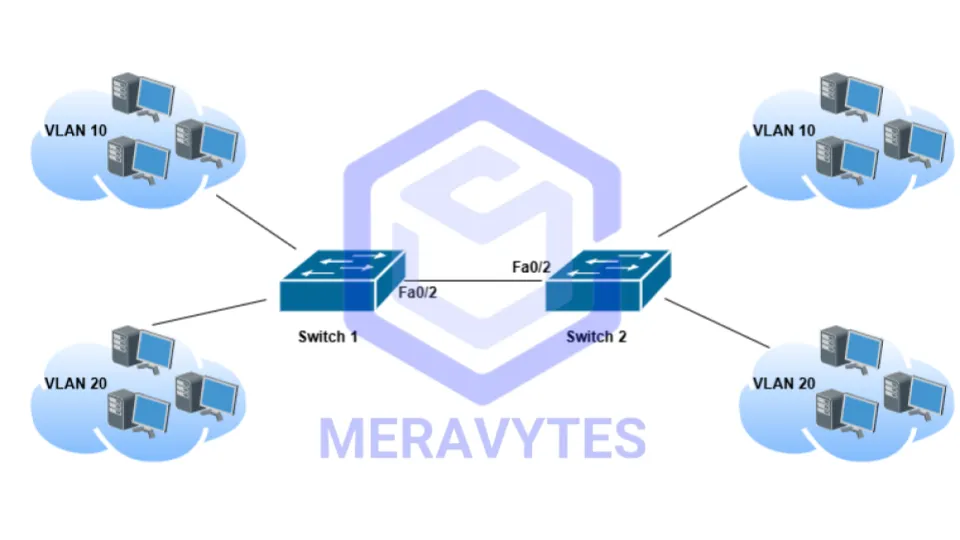
Essential Cisco CLI Commands
By Meravytes | January 26, 2025
Cisco routers and switches are integral components of modern network infrastructure, mastering their Command Line Interface (CLI) is crucial.

Deepfakes: The Double-Edged Sword of AI Innovation
By Meravytes | December 26, 2024
Deepfake technology represents one of the most fascinating yet controversial advancements in artificial intelligence (AI).

Mastering VLSM: How to Calculate Variable Length Subnet Masks Manually?
By Meravytes | November 26, 2024
Variable Length Subnet Mask (VLSM) is a powerful technique used to optimize IP address allocation in a network.

Dark Web Monitoring: A Critical Component of Threat Intelligence
By Meravytes | September 28, 2024
For organizations, understanding and monitoring the dark web is essential to enhance their threat intelligence capabilities and bolster their cybersecurity defenses.
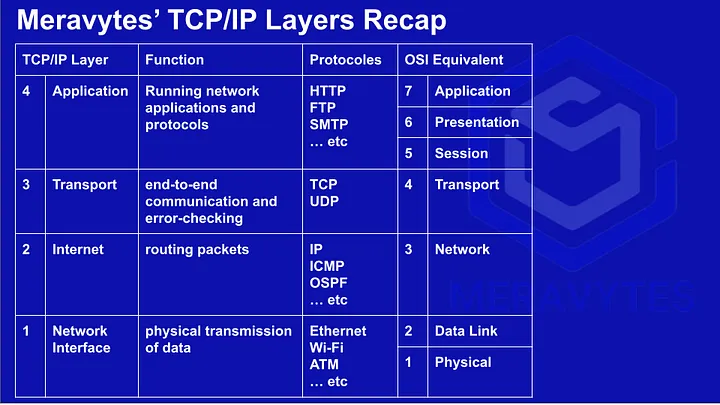
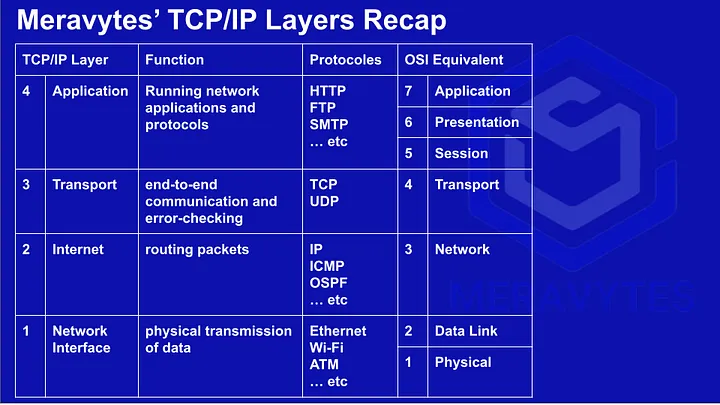
Understanding TCP/IP: The Backbone of the Internet
By Meravytes | September 17, 2024
The Transmission Control Protocol/Internet Protocol (TCP/IP) suite is the foundational framework for communication across networks, particularly the Internet.

Ransomware-as-a-Service (RaaS)
By Meravytes | August 08, 2024
Ransomware attacks have become a formidable threat in the digital landscape, wreaking havoc on organizations and individuals alike.

The Rise of AI-Driven Phishing Attacks: A New Era in Cybersecurity Threats
By Meravytes | August 01, 2024
In the ever-evolving landscape of cybersecurity, a new and formidable threat has emerged: AI-driven phishing attacks.

Unveiling the Threat: Understanding and Defending Against Phishing Attacks
By Meravytes | July 28, 2024
In today’s interconnected world, where digital communication dominates our daily lives, the threat of phishing attacks looms larger than ever.

Zero Trust Architecture: Enhancing Cybersecurity in a Perimeter-less World
By Meravytes | July 25, 2024
In an era where the traditional network perimeter is dissolving, the concept of Zero Trust Architecture (ZTA) has emerged as a game-changer in the cybersecurity landscape.
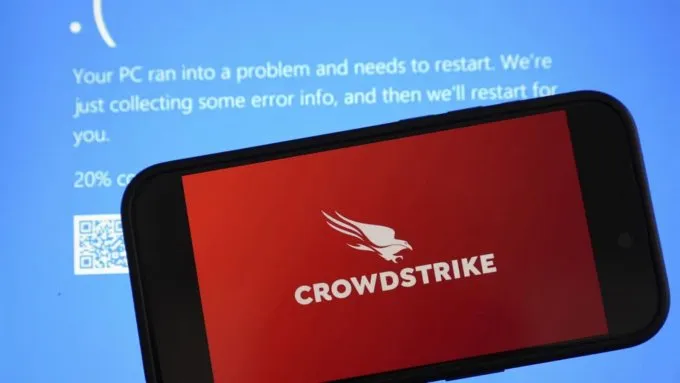
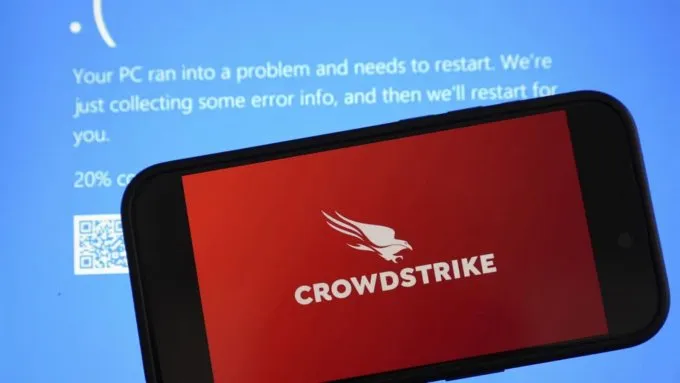
Major Global IT Outage Caused by Faulty CrowdStrike Update
By Meravytes | July 20, 2024
A recent update from cybersecurity firm CrowdStrike resulted in widespread disruptions, affecting Windows machines globally.

The Titans of Cyber Destruction: Exploring the Most Dangerous Malware in Cybersecurity History
By Meravytes | July 18, 2024
In the ever-evolving landscape of cybersecurity, certain pieces of malware have etched their names into history.

How to Reset the Root Password on Your FortiSIEM Appliance
By Meravytes | July 7, 2024
Losing access to your FortiSIEM appliance due to a forgotten root password can be stressful, but resetting it is straightforward if you follow these steps carefully.

CherryBlos Malware: A Sophisticated Cyber Espionage Threat
By Meravytes | July 30, 2023
CherryBlos is a highly sophisticated malware believed to be developed and utilized by a state-sponsored cyber espionage group.
AlienFox Malware
By Meravytes | April 12, 2023
AlienFox is a type of malware that has been discovered by cybersecurity researchers in recent years.
Rorschach Ransomware
By Meravytes | April 11, 2023
Rorschach ransomware designed to encrypt files on infected devices and demand a ransom payment in exchange for the decryption key.

Typhon Reborn Stealer Malware
By Meravytes | April 10, 2023
Typhon Reborn Stealer is a type of Trojan that is designed to steal sensitive information from infected devices.

Mélofée Malware
By Meravytes | April 10, 2023
One of the key features of the Mélofée malware is its ability to remain hidden on the infected device, making it difficult to detect and remove.

Advanced Evasion Strategies: The Evolving Threat to Cybersecurity and How to Protect Against Them
By Meravytes | April 09, 2023
Advanced evasion strategies are a set of techniques used by cybercriminals to evade detection and gain access to target systems.

Advanced Evasion Strategies: The Evolving Threat to Cybersecurity and How to Protect Against Them
By Meravytes | April 08, 2023
Cryptocurrency companies have been hit by yet another security breach, this time via a supply chain attack on the popular 3CX communications platform.

Western Digital Faces Critical Data Disruptions Following Network Security Breach
By Meravytes | April 07, 2023
The breach occurred when an unknown attacker gained unauthorized access to Western Digital's internal network, allowing them to bypass security measures and access sensitive information.

LockBit 3.0 Ransomware
By Meravytes | April 06, 2023
LockBit 3.0 is the latest version of a dangerous ransomware that has been causing major disruptions around the world.

KEYPLUG Backdoor
By Meravytes | April 05, 2023
KEYPLUG is a type of backdoor malware that can be used by attackers to gain unauthorized access to systems and networks.
3CX Supply Chain Attack
By Meravytes | April 04, 2023
The 3CX Supply Chain Attack is a recent cybersecurity incident that has caught the attention of security experts and organizations alike.

Super FabriXss Vulnerability in Microsoft Azure SFX
By Meravytes | April 03, 2023
This vulnerability could potentially allow attackers to execute arbitrary code on the affected system.
aCropalypse Bug
By Meravytes | April 02, 2023
A recent privacy flaw has been identified in the built-in screenshot tool in Windows, known as "aCropalypse."

New MacStealer Malware
By Meravytes | April 01, 2023
New MacStealer is a type of malware that is specifically designed to steal sensitive data from Mac users.
ShellBot DDoS Malware
By Meravytes | March 31, 2023
ShellBot is a type of DDoS malware that is used to launch attacks against websites and servers, causing them to become unavailable to users.

RIG Exploit Kit
By Meravytes | March 30, 2023
The RIG Exploit Kit is a tool used by cybercriminals to exploit vulnerabilities in computers and install malware, such as ransomware or trojans.
Emotet Malware
By Meravytes | March 29, 2023
Emotet is a notorious malware that has been causing havoc in the cyber world since 2014. due to its ability to evade detection.

CatB Ransomware's Evasion Techniques
By Meravytes | March 28, 2023
CatB ransomware uses a multi-stage infection process, which involves several steps to infect the targeted system.

Mispadu Banking Trojan
By Meravytes | March 27, 2023
Mispadu is a dangerous banking Trojan that is designed to steal sensitive information such as banking credentials and other personal data from its victims.

DotRunpeX Malware
By Meravytes | March 26, 2023
This malware is a type of Trojan that targets Windows systems and is designed to steal sensitive information from the victim's computer.

U.K. National Crime Agency's Fake DDoS-For-Hire Sites: A New Tactic to Catch Cybercriminals
By Meravytes | March 25, 2023
The U.K. National Crime Agency (NCA) has taken a bold new approach to catch cybercriminals who engage in Distributed Denial of Service (DDoS) attacks.

SYS01stealer Malware
By Meravytes | March 21, 2023
SYS01stealer is a form of malware-as-a-service (MaaS) that is designed to steal sensitive information from infected systems.

PureCrypter Malware
By Meravytes | March 20, 2023
PureCrypter is a form of ransomware, a type of malware that encrypts the victim's files and demands payment in exchange for the decryption key.

S1deload Malware
By Meravytes | March 19, 2023
S1deload is a type of malware that is designed to steal sensitive information from infected systems.

PlugX Trojan
By Meravytes | March 18, 2023
The PlugX Trojan is a type of malware that is designed to give remote attackers complete control over a victim's computer system.

Parallax RAT
By Meravytes | March 17, 2023
Parallax RAT, also known as AVE_MARIA or WARZONE RAT, is a Remote Access Trojan (RAT) that allows attackers to gain complete control over a victim's computer.

IceFire Ransomware
By Meravytes | March 16, 2023
IceFire ransomware is particularly dangerous because it not only encrypts files but also steals sensitive data and exfiltrates it to the attackers' servers.

ScrubCrypt
By Meravytes | March 15, 2023
ScrubCrypt is particularly dangerous because it not only encrypts data but also destroys the backup files, making it almost impossible to recover without paying the ransom.

FortiGate Application-Specific Integrated Circuits (ASICs)
By Meravytes | March 14, 2023
Fortinet's FortiGate firewall devices are equipped with Application-Specific Integrated Circuits (ASICs) that are designed to perform network security functions at high speeds.
The Most Dangerous APT Groups
By Meravytes | March 13, 2023
In this article, we will explore some of the most dangerous APT groups currently active.
EX-22 Tool
By Meravytes | March 12, 2023
the EX-22 tool is designed to help cybersecurity professionals and penetration testers identify vulnerabilities and weaknesses in their networks and systems.

Client-Side Encryption (CSE) in Gmail and Google Calendar
By Meravytes | March 11, 2023
Client-Side Encryption (CSE) is a technique used to secure data at rest, where data is encrypted before it leaves the client device.

Critical Flaw in Fortinet Products: CVE-2023-25610 Exposes Networks to Cyber Threats
By Meravytes | March 10, 2023
A new vulnerability, known as CVE-2023-25610, has been discovered in several Fortinet products, which could potentially allow an attacker to execute arbitrary code.
FortiGate SD-WAN solution
By Meravytes | March 09, 2023
Software-defined WAN (SD-WAN) is a networking technology that allows organizations to simplify the deployment and management of their WAN infrastructure.

Bitdefender's Free Decryptor for MortalKombat Ransomware
By Meravytes | March 08, 2023
Cybersecurity firm Bitdefender has developed a free decryptor for MortalKombat ransomware victims, allowing them to recover their encrypted files without paying a ransom.
BlackLotus Botnet Malware
By Meravytes | March 05, 2023
BlackLotus malware, also known as the Russian DDoS botnet, is a type of malware that is primarily used for distributed denial of service (DDoS) attacks.

The Best Cisco Certifications For Network And Security Engineers
By Meravytes | March 03, 2023
These certifications are designed to help IT professionals validate their skills, knowledge, and expertise in designing, implementing, and troubleshooting Cisco network solutions.

FortiGate Security Processing Units (SPUs)
By Meravytes | March 02, 2023
FortiGate SPUs are specialized hardware components that are specifically engineered as ASIC circuits to enhance both the performance and security.

Trojanized PyPI Packages
By Meravytes | March 01, 2023
the recent trend of Trojanized PyPI packages is becoming a serious concern for developers and users alike.

Network Traffic Analysis (NTA) Techniques
By Meravytes | February 28, 2023
Network traffic analysis (NTA) is a method of identifying and responding to anomalous network traffic behavior.
MyloBot Botnet
By Meravytes | February 28, 2023
MyloBot is capable of performing a variety of malicious activities, including stealing credentials, launching DDoS attacks, executing remote code, and spreading itself to other devices on the same network.

New Vulnerabilities Affecting Apple Products
By Meravytes | February 25, 2023
Recently, Apple announced the discovery of several new vulnerabilities affecting iPhone, iPad, and Mac devices.

Auditing Kubernetes
By Meravytes | February 24, 2023
Kubernetes is a popular and widely used container orchestration platform, that enables the deployment, scaling, and management of containerized applications.

ReverseRAT Backdoor: A Dangerous Cybersecurity Threat
By Meravytes | February 23, 2023
ReverseRAT is a type of remote access Trojan (RAT) that provides attackers with a backdoor into a compromised system.

Samsung Introduces New Feature to Protect Users from Zero-Click Malware Attacks
By Meravytes | February 22, 2023
Samsung, one of the world's leading technology companies, has announced a new feature that will help protect users from zero-click malware attacks.

Twitter Limites SMS-based Two-factor Authentication
By Meravytes | February 22, 2023
Twitter previously offered SMS-based two-factor authentication as an additional layer of security for user accounts.

RambleOn Android Malware: A Threat to Mobile Security
By Meravytes | February 20, 2023
RambleOn is a malicious program that is primarily distributed through third-party app stores, disguised as legitimate applications.

Fortinet Issues Security Updates To Patch 40 Vulnerabilities In Its Products
By Meravytes | February 19, 2023
Fortinet, recently released patches for 40 vulnerabilities affecting various products in its portfolio.
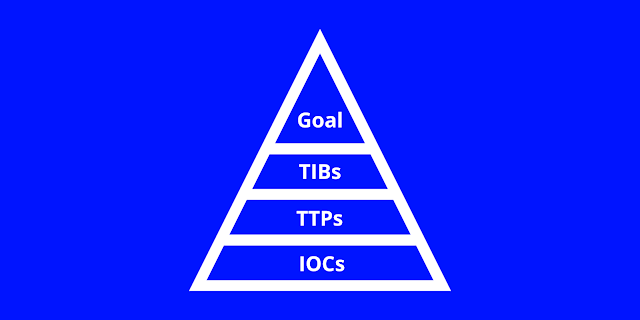
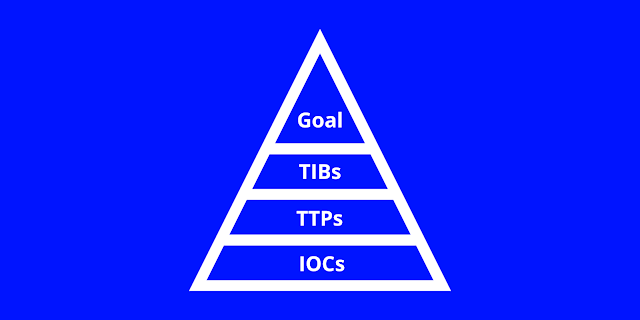
Pyramid of Pain
By Meravytes | February 18, 2023
The Pyramid of Pain is a concept used in cybersecurity to prioritize and categorize different types of threat intelligence.
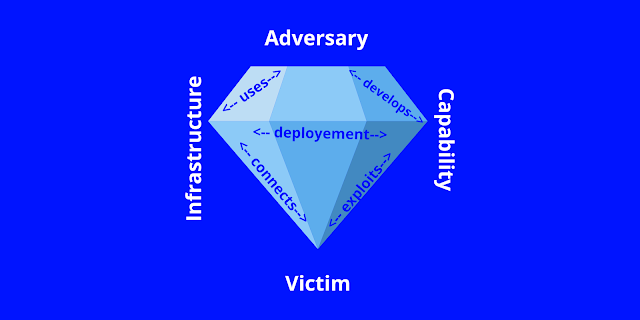
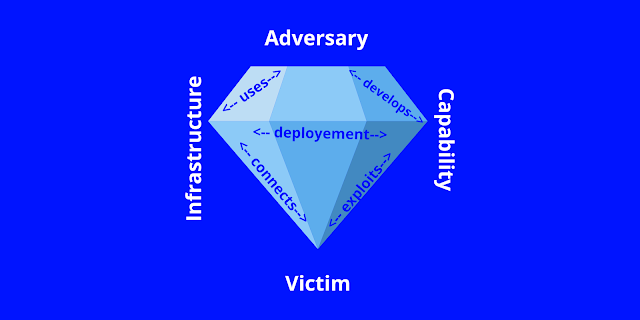
Diamond Model of Intrusion Analysis
By Meravytes | February 18, 2023
The Diamond Model of Intrusion Analysis is a methodology for investigating and analyzing cyberattacks.

Cyber Threat Intelligence: Understanding and Mitigating Cybersecurity Threats
By Meravytes | February 18, 2023
Cyber Threat Intelligence (CTI) is an emerging field that focuses on identifying, analyzing, and mitigating cyber threats.

MITRE Cybersecurity Projects
By Meravytes | February 17, 2023
MITRE Corporation is a non-profit organization that manages a variety of projects related to cybersecurity.

Most Common Terms Used By Network And Security Engineers
By Meravytes | February 17, 2023
Network and security engineers encounter a variety of technical terms in their work, including logs, alerts, DMZ, packets, configurations, and ping, ...

OpenVAS - Open Vulnerability Assessment System
By Meravytes | February 17, 2023
OpenVAS, short for Open Vulnerability Assessment System, is a popular open-source vulnerability scanner.

FortiGate: A Comprehensive Network Security Solution
By Meravytes | February 12, 2023
Fortinet's FortiGate is a network security solution that offers a comprehensive set of security features for organizations of all sizes.

Gootkit Malware: Understanding and Mitigating the Threat
By Meravytes | February 11, 2023
Gootkit is a type of banking Trojan malware that targets online banking users.
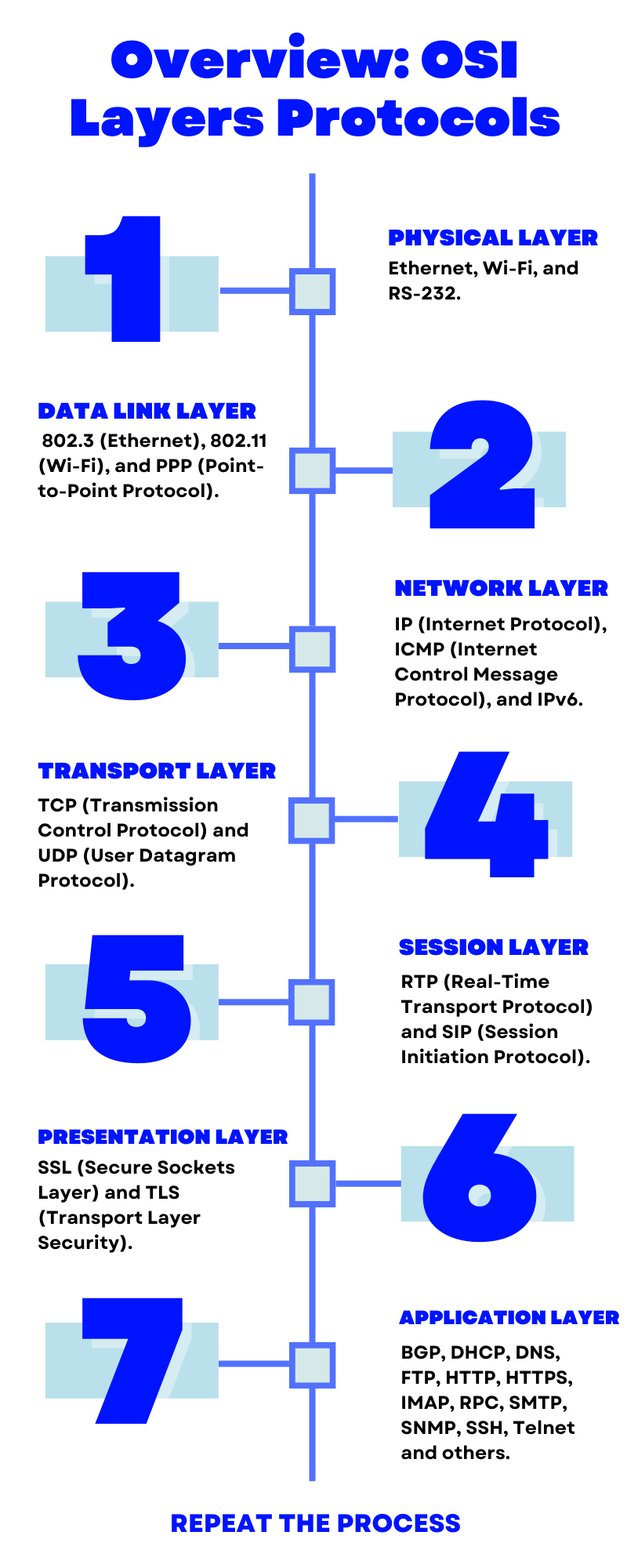
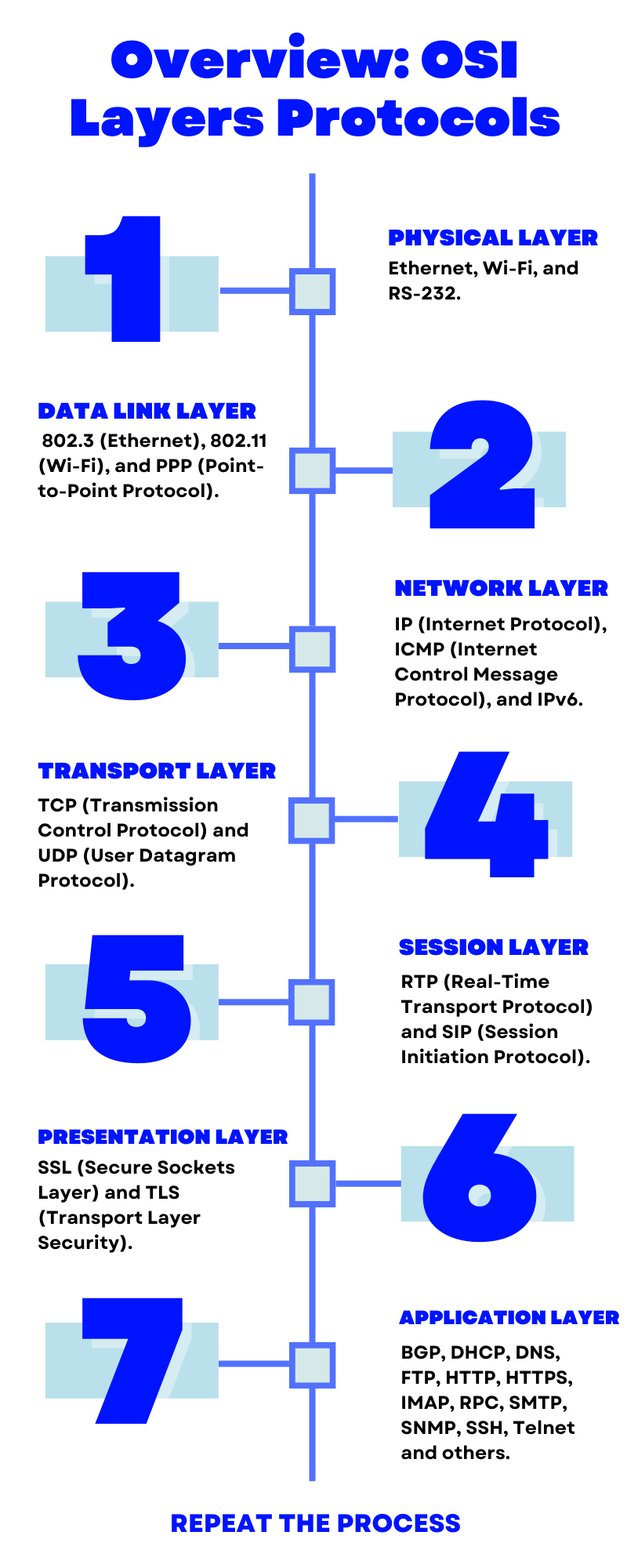
Overview: OSI Layers Protocols
By Meravytes | February 11, 2023
The seven layers of the OSI (Open Systems Interconnection) model are a theoretical framework for the design of communication protocols.

Wireshark For Pentesting
By Meravytes | February 07, 2023
Wireshark is a powerful and widely used open-source tool for network analysis and troubleshooting.

PixPirate Android Banking Trojan
By Meravytes | February 05, 2023
PixPirate is a type of malware that is specifically designed to steal sensitive information, such as usernames, passwords,...

Titan Stealer Malware: Understanding and Protecting Against the Threat
By Meravytes | February 04, 2023
Titan Stealer malware is a type of malicious software that is designed to steal sensitive information from infected computers.

20 Interview Questions For Networking And Security Jobs
By Meravytes | February 04, 2023
What are some of the key security threats facing networks today?Some common security threats include malware, phishing attacks ...

Realtek RTL8153/RTL8154 USB To Ethernet Controllers Vulnerability
By Meravytes | February 03, 2023
A vulnerability was discovered in Realtek RTL8153/RTL8154 USB to Ethernet controllers that could allow attackers to remotely execute code and take control of affected devices.

Cybersecurity 101
By Meravytes | February 03, 2023
The goal of cybersecurity is to ensure the confidentiality, integrity, and availability (CIA) of sensitive information and systems.
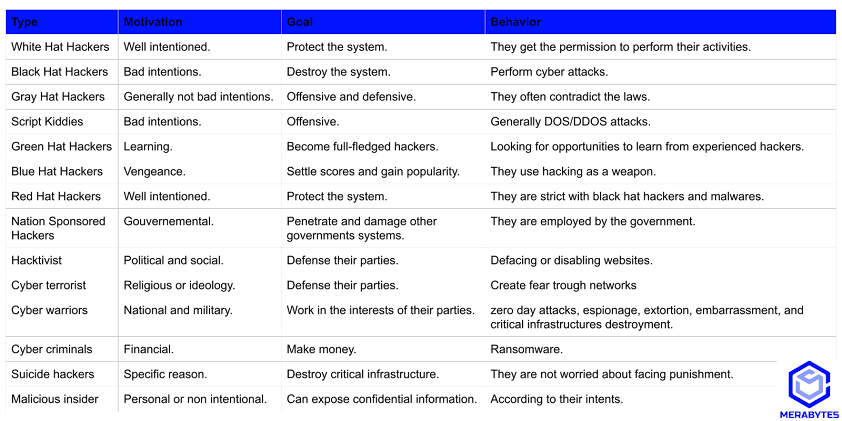
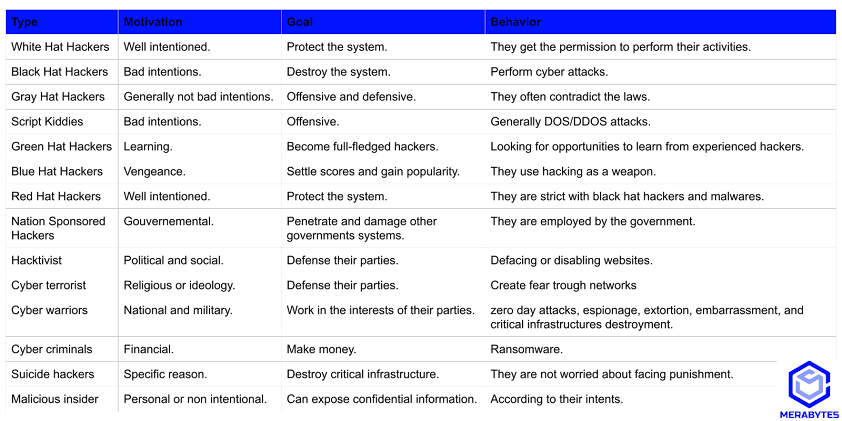
Threat Actors
By Meravytes | January 31, 2023
Threat actors, bad entities aka hackers nowadays, are not limited to IT-savvy people, they are typically everyone who is always looking for gaps.

QNAP Security Updates To Patch The Zero-day Vulnerability In QTS 5.0.1 And QuTS hero h5.0.1 Devices
By Meravytes | January 31, 2023
Qnap Systems, Inc., has released its latest security update covering a critical vulnerability that could lead to arbitrary code injection in its network-attached storage (NAS) devices.